-
Cisco Router Generate Rsa Key 1024카테고리 없음 2020. 8. 29. 00:37
Router1(config)#crypto key generate rsa The name for the keys will be: Router1.oreilly.com Choose the size of the key modulus in the range of 360 to 2048 for your General Purpose Keys. Choosing a key modulus greater than 512 may take a few minutes. How many bits in the modulus 512: 1024 Generating RSA keys. Jun 11, 2019 SW1 ( config)# crypto key generate rsa. How many bits in the modulus 512: 1024% Generating 1024 bit RSA keys, keys will be non-exportableOK Set the size of key to 1024 bits. If your Cisco Switch is running an older version of Cisco IOS image, then it is extremely recommended that you upgrade to latest Cisco IOS. I have issued the command crypto key generate rsa general-keys modulus 2048. MY router is 1024 bits. User Experience Enhancements As part of the Cisco Common.
Configuration of SSH on Cisco Switch in Packet Tracer 2019
This Article is about the configuration of SSH on Cisco Switch. You can configure SSH on Cisco devices very easily using these simple steps:
- Crate a Packet Tracer Topology Lab
- Basic IP Setting for connectivity
- Set hostname and domain-name on Switch
- Set console and enable password for SSH login
- Generate the RSA Keys
- Setup the Line VTY configurations
- Create the username password for SSH access from PC
- Verify SSH access
For the configurations of SSH in packet tracer on Cisco switch, you are required to follow the above steps. Let start and perform these steps one by one. (Learn what is PSSH)
Crate a Packet Tracer Topology Lab
Our first step is to open the packet tracer and need to create a simple lab. For this topology we will use only one switch and a PC. Simply drag these two items on dashboard. Now we will connect them with straight through connection.
Basic IP Setting for connectivity
The next step is assign the suitable IP setting to these devices. For keeping it simple and making basic connectivity we will assign just two IP address to these device. We will assign the IP address to PC. For this will open the PC setting and then IP configuration. Here we will assign an IP address to host, in our case we are going to assign it 192.168.1.1 with the default gateway. For default gateway we will assign the IP address 192.168.1.10. We assign the second IP address to our Vlan1 interface on switch. And its IP address will be the gateway of host that is 192.168.1.10. For this we will use the basic commands.
Switch> enableSwitch# config tSwitch(config)#interface vlan 1Switch (config-if)# ip address 192.168.1.10 255.255.255.0Switch (config -if)#no shutOnce you done with basic IP setting, you can verify the connectivity by pinging the interface vlan1 IP from host.
Set host-name and domain-name on Switch
For SSh configurations you need to configure a host-name and domain-name for your switch you can do this with these simple commands.
Switch # config tSwitch (config)#hostname SW1SW1 ( config)#ip domain-name w7cloud.comSet console and enable password for SSH login
For SSH access it is required that you must configure the console and enable password on your cisco switch. You can set these two passwords with following commands.
SW1 ( config)#line console 0SW1(config-line)#password ciscoSW1(config -line)#logging synchronousSW1(config- line)#login localSW1 (config- line)#exitSW1 # enable secret cisco
Generate the RSA Keys
Your Cisco switch must have RSA keys that for the SSH process. You can generate the RSA keys with following command:
SW1 ( config)# crypto key generate rsaHow many bits in the modulus [512]: 1024
% Generating 1024 bit RSA keys, keys will be non-exportable…[OK]
Set the size of key to 1024 bits.
If your Cisco Switch is running an older version of Cisco IOS image, then it is extremely recommended that you upgrade to latest Cisco IOS.
Setup the Line VTY configurations
For the configuration of SSH on cisco switch you need the following line vty configurations, and input transport is required to set to SSH. Set the login-to-local, & password to 7.
sw1 ( config)#line vty 0 4sw1 ( config-line)#transport input sshsw1( config -line)#login local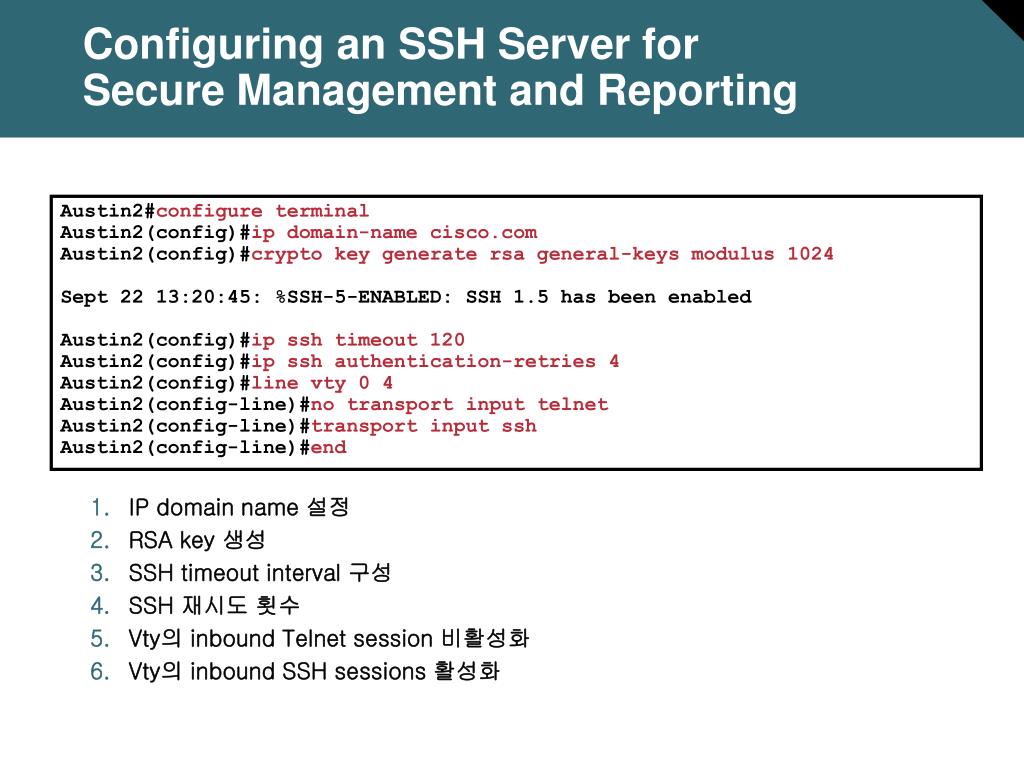
sw1(config- line)#password 7sw1(config- line ) #exit
Create the username password for SSH access from PC
If you do not have a username for SSH access you need to create a username. You can do it with this simple command:
Sw1# config tsw1 (config ) # username w7cloud password ciscoMake sure the password encryption services is enabled on your switch, this service will encrypt your password, & when you do “sh run”, you’ll see only the encrypted password, not clear text password.
SW1# service password-encryption
Verify SSH access from Host
Once you done with the above configurations you can test all these configuration by creating a SSH connection from Host. You do it the command ssh –l <username> <IP address>. Open the host command prompt and use the command
C:>ssh -l waqas 192.168.1.10
Crypto Key Generate Rsa 1024

It will ask for password, provide the password that you created with this username in previous steps. Then it asked for console password and then you need to provide the enable password. Now you are in your Cisco switch. You can perform switch configurations from your host.
Generate Rsa Key Pair
From the switch, if you use the command ‘sh ip ssh’, it will also confirm that SSH is enabled on this cisco swith.
Patch Rsa 1024 Public Key
For better understanding please watch the video and like it.
I hope this will be a helpful for you, please share your comments. If you like this then share this on social media. Thank you for reading this..!Guide on Cisco Router Configuration for Beginners
Rsa 1024 Crack
Related: 4 Best SSH Client Used by Professionals